文章来源:
https://xz.aliyun.com/t/5249?page=1&entryScene=zhida_05_001&jump_from=1_13_18_00
手机端
我这里手机上的APP没用他文中的Google Authenticator,我用的Authy,他可以兼容前者。
服务器上安装 Google authenticator
sudo apt-get install libpam-google-authenticator
google-authenticator它会提示你是否生成基于时间的 Token,这时候根据你的喜好选择,我这里选择是,输入Y。
此时会出现一张二维码图片,用上面的手机APP扫描出现的二维码,然后填写相关信息,此时就会多出一个账号信息(六位数的动态码),另外记得妥善保存你的Emergency Key。
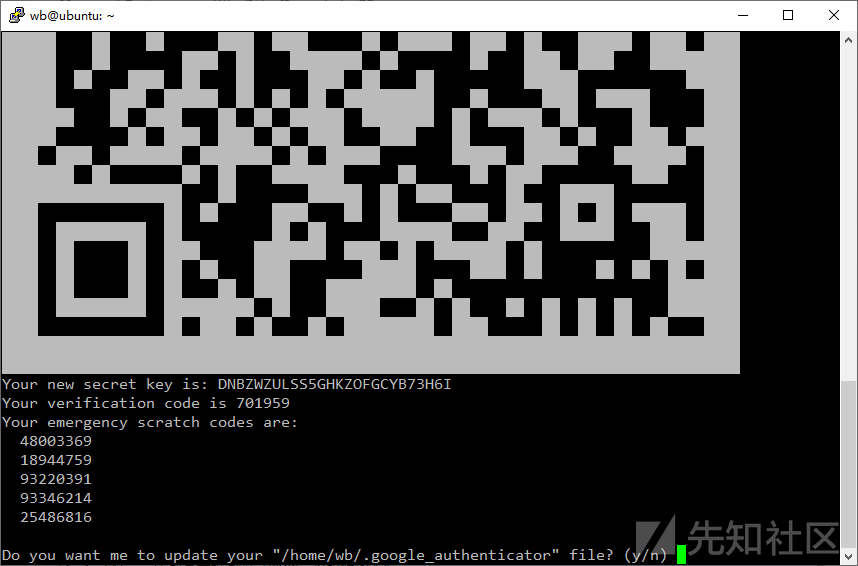
Do you want me to update your "/home/wb/.google_authenticator" file? (y/n),输入Y。我这里由于登录的用户和他不一样,但是大同小异。
Do you want to disallow multiple uses of the same authentication
token? This restricts you to one login about every 30s, but it increases
your chances to notice or even prevent man-in-the-middle attacks (y/n) yBy default, a new token is generated every 30 seconds by the mobile app.
In order to compensate for possible time-skew between the client and the server,
we allow an extra token before and after the current time. This allows for a
time skew of up to 30 seconds between authentication server and client. If you
experience problems with poor time synchronization, you can increase the window
from its default size of 3 permitted codes (one previous code, the current
code, the next code) to 17 permitted codes (the 8 previous codes, the current
code, and the 8 next codes). This will permit for a time skew of up to 4 minutes
between client and server.
Do you want to do so? (y/n) n
If the computer that you are logging into isn't hardened against brute-force
login attempts, you can enable rate-limiting for the authentication module.
By default, this limits attackers to no more than 3 login attempts every 30s.
Do you want to enable rate-limiting? (y/n) y配置SHH
/etc/pam.d/sshd末尾追加一行auth required pam_google_authenticator.so nullok
注意:
nullok的意思是这项验证是可选的,如果你没有TOTP令牌的话,仍然可以使用SSH密码和密钥登录,我们为了保险起见先使用这个,等到配置好了之后就可以去掉了。
吧/etc/ssh/sshd_config 的 ChallengeResponseAuthentication设置为Yes
sudo systemctl restart sshd,重启一下 SSH 服务
再次连接就需要二次验证了
Can you be more specific about the content of your article? After reading it, I still have some doubts. Hope you can help me. https://accounts.binance.com/pt-BR/register-person?ref=YY80CKRN